Woodbury, NY—We get tons of e-mail and most gets tossed, but this intriguing snippet from the Verge snapped us to attention. The alarming headline reads: “Security researchers find that DSLR cameras are vulnerable to ransomware attack.”
The text then gives a brief summary of a report posted by Check Point Research, a cyber threat intelligence company. It provides protective Check Point software as well as analyzes global cyber-attack data stored on ThreatCloud.
Ransomware & DSLRS
The original August 11, 2019 article by lead researcher Eyal Itkin is provocatively titled Say Cheese: Ransomware-ing a DSLR. It describes in excruciatingly geeky detail how they were able to install malicious software on a hapless Canon EOS 80D. They did so via its USB and Wi-Fi connectivity.
One key entry point is the camera’s Picture Transfer Protocol (PTP). This is an attractive target because it’s unauthenticated; supports dozens of different complex commands; and also can be exploited over USB and Wi-Fi. The latter makes cameras accessible to nearby attackers.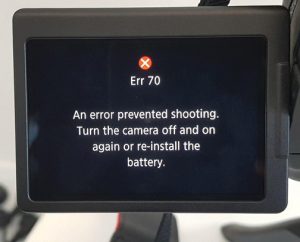
Moreover, to hack the camera, Check Point tried a variety of different approaches. They included obtaining firmware and firmware updates; reversing the PTP layer; accessing the PTP Handler API; sending various commands to the buffer overflow; and also gaining code execution.
In addition, once they had access the next step was to encrypt the files stored on the camera via the PTP command for remote firmware update and its AES encryption. After encrypting all the files on the SD card, the ransomware displays the dreaded ransom message to the user.
The good news: All the vulnerabilities above were duly reported to Canon on March 31, 2019, and Canon confirmed them on May 14, 2019. Furthermore, Check Point Research verified and approved Canon’s patch on July 8, 2019; Canon then published the patch as part of an official security advisory on August 6, 2019. 
However, there is bad news. The research revealed multiple critical vulnerabilities in the Picture Transfer Protocol.
In fact, it showed that virtually any smart device—including a camera—is susceptible to attack by bypassing the encryption and verification functions in the firmware itself. Stay tuned for further developments.